Security and simplicity drive enterprise investment in the IoT
Although complexity and security have slowed adoption, taking advantage of the money-saving benefits enabled by the Internet of Things is top-of-mind for enterprise decision-makers. With the pending commercialization of standards-based 5G networks, support for secure, massively-scaled IoT deployments is quickly becoming a valuable reality.
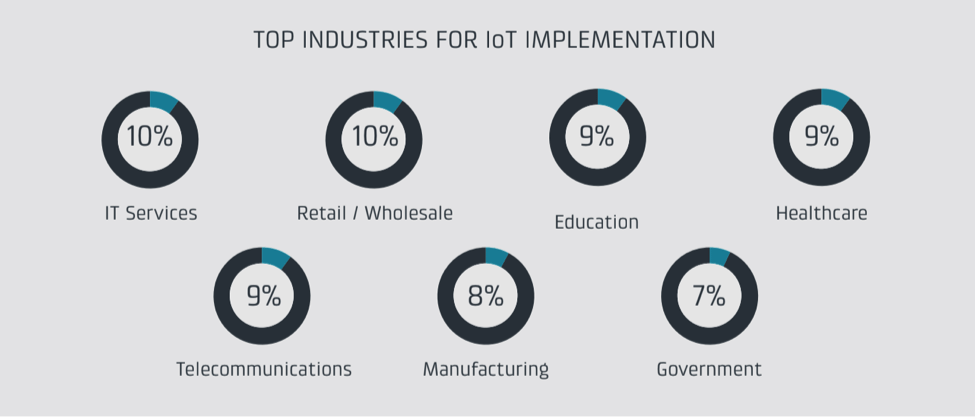
Based on a survey of 400 IT professionals in the U.S., Canada and the U.K., Cradlepoint found in its State of IoT 2018 report that successful enterprise IoT projects require an overall shift toward mobile connectivity, the cloud and automation; this move requires a more flexible enterprise WAN with an elastic edge that takes full advantage of increasing bandwidth and lower latency. The top industries for IoT implementation, according to the report, are IT services, retail/wholesale, education, telecommunications, manufacturing, government and healthcare.
During Mobile World Congress 2018, Cradlepoint demonstrated what Lindsay Notwell, VP, 5G Strategy and Worldwide Carrier Operations, described as a “remote subject matter expert” healthcare application. “Instead of having very expensive people out in the field, you’re actually able to leverage, in a call center or a doctor’s home office, that ability for a highly-skilled remote subject matter expert and then less-skilled, less-expensive hands with the right equipment and the right connectivity at the end site.”
Click here to watch the demonstration of remote healthcare.
Cradlepoint VP, IoT Strategy and Business Development, Ken Hosac described how the company’s customers —”distributed enterprise, these are enterprises that have branch offices or vehicles or digital signage”— need to be prepared for a wide variety of IoT related requirements that “might go all the way from video cameras with facial recognition to other customer analytics sensors.”
Ahead of MWC, Cradlepoint launched its NetCloud Solution Package for IoT, a cloud-based services suite with Software-Defined Perimeter technology for secure device-to-cloud connectivity. Hosac explained Software-Defined Perimeter security uses encrypted, perimeter-secured virtual overlays with private IP addressing to protect IoT devices. “Software-Defined Networking is about authenticating first and connecting second,” he said. “If you can’t authenticate at the device or at the local side, you don’t even get to see the network.”
According to a 2017 survey report by James Brehm and Associates, 65 percent of 416 respondents listed security as a barrier to scaling IoT implementations. “Despite the huge growth in IoT deployments, security and management-related costs remain top concerns for IT organizations,” firm founder James Brehm wrote. “Cradlepoint has taken a service-oriented approach to addressing these challenges by combining cloud management, routing and security features, along with purpose-built hardware, into a single cloud service with 24×7 vendor support.”
5G and the IoT
Last year the 3GPP adopted a standard for non-standalone 5G New Radio, which integrates updated RAN components with an LTE core. Later this year, the group is set to adopt a standalone 5G NR variant that defines a totally new RAN and core network. For both flavors of 5G, there are three primary use cases: enhanced mobile broadband, mission critical communications and massive IoT.
According to Cradlepoint’s report State of 5G 2017 & Beyond, early standards-based 5G deployments will be geared toward fixed wireless access to serve increased demand for mobile data with faster broadband speeds for enterprise and consumer users. The continued evolution of 5G will see wide-ranging support for all manner of IoT applications, including use cases like smarter metering that don’t require much throughput or latency and, on the other end of the scale, data-intensive, latency-sensitive use cases like real-time facial recognition. Massive IoT will come with devices that use very little energy and have very long battery life, increasingly low cost devices, device density and an enhanced cellular footprint.
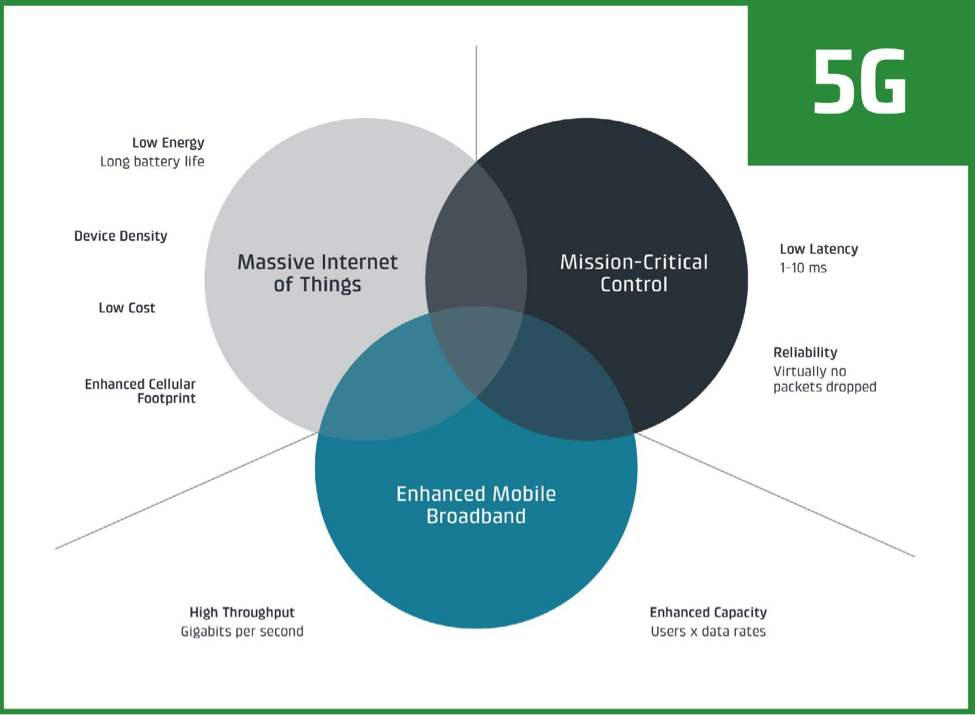
“5G has some exciting native capabilities for IoT,” Hosac said. “What we’re seeing, again with our distributed enterprises, is they have at their locations a blend of traditional devices and IoT devices, some they are low power, some of them are high bandwidth. On the WAN side, they just need it to be really, really fast and very, very reliable.”
As 5G continues to develop and become commercially available, Notwell identified improvements to latency “as a little bit of a sleeper. The requirements becomes now down to, in some cases, single-digit milliseconds. The traditional model is I have this centralized firewall. If I’m taking the traffic from the edge to that centralized firewall to the destination, which nowadays is out on the internet, that trombone effect introduces a lot of latency.” By distributing functions like Software-Defined Perimeter, “It also places the security out in the cloud…to able to deliver that secure environment and still maintain the latency improvements that 5G wants to promise.”
Click here to see Hosac and Notwell discuss Cradlepoint’s view on 5G and the IoT with RCR Wireless News during Mobile World Congress 2018.

